We may earn money or products from the companies mentioned in this post.
Although the term has gone through several changes in meaning over the years, today most people use the term “hacker” to describe a person who breaks into computer systems for fun and profit. While some hackers practice their electronic breaking and entering for legitimate profit (for example, working as computer security consultants) or as a fun intellectual exercise, the ones most commonly found in role-playing games usually have darker agendas. Once inside a secure system, the hacker can steal valuable or classified information or take control of the system and make it do their bidding.
Likely Stories: Any story with widespread computer technology. Although the term has been used since the 1960s to describe computer hobbyists, the kind of hacker we’re talking about didn’t really come into his own until computers became widespread in the 1980s. Modern-day hackers are most likely to show up in stories where characters regularly break into (or provide security for) places with high-tech security or where characters regularly need access to secure information. The most common use of the hacker as a player character occurs in the cyberpunk genre, though they can also be found in some other subgenres of science fiction.
The Name Game: Most hackers prefer to be called by their screen name, or online alter-ego. These names range from the incredibly egotistical to the obnoxiously nerd-clever to the just plain stupid. Some hackers use the names (or variations on the names) of popular fictional characters as their screen names. In general, the intent of screen names is to make the hacker sound much cooler than he or she really is. In reality, most hackers are nerdy white kids, and it may be tempting to give the hacker an incredibly dorky real name. There is no particularly convincing reason to resist this temptation.
The Numbers: Hacking requires a combination of obscure knowledge, problem solving ability, and instinct, which means any hacker who wants to be successful needs a high Brain Number. Since spending most of your day sitting in front of a computer isn’t exactly an active lifestyle, most hackers will have relatively low Body Numbers. A hacker’s Nerve Number will depend on hacker’s style and possibly the time period of the game. Modern-day hackers can get everything they need online, and therefore don’t need to interact with people very often. This often makes them socially awkward (reflected by a low Nerve Number or appropriate Weakness). In the old days, before everything was connected to the internet, things were a bit tougher. Hackers had to get passwords, dial-up numbers, and even operating system manuals from the source. This involved dumpster diving, breaking and entering, and something called “social engineering,” which means tricking someone into revealing information they’re supposed to keep secret. In order to sound convincing in their social engineering attempts and avoid chickening out when it’s time to skulk about, old school hackers need a good Nerve Number.
Suggested Jobs: Blogger, Computer Engineer, Computer Security Expert, Conspiracy Theorist, Cryptographer, Cybercriminal, Decker, Identity Thief, Internet Entrepreneur, Keyboard Cowboy, Netrunner, Network Administrator, Phreaker, Professional Gamer, Programmer, Research Assistant, SEO Specialist, Spammer, Spy, Student, Techno Pagan, Web Designer
Suggested Gimmicks: Contacts, Ghost in the Machine, Hide in Plain Sight, Insider Information, Internet Celebrity, Magic Touch, Photographic Memory, Read About It On Usenet, Rich, Sounds Honest, There’s An App For That, Thinks In Code, Third Time’s A Charm, Wonderful Toys
Suggested Weaknesses: ADD, Addiction, Bad Information, Clumsy, Delusional, Disabled, It Worked Fine On My Machine, Kid, OCD, Outdated Knowledge, Paranoid, Physically Weak, Pornado Magnet, Sleep Disorder, Socially Awkward, Troll Magnet, Weak Grasp on Reality
Suggested Skills: Breaking & Entering, Computer Architecture, Comic Book Trivia, Communications, Conspiracy Theory, Cryptography, Data Mining, Day Trader, Dumpster Diving, Ebay, Eavesdropping, Electronics, Fast Talking, Game Theory, Gamer Geek, Google-Fu, Graphics, Ham Radio Operator, Logic, Math, Memes, Netiquette , Nigerian Schemes, Peer-to-Peer Protocol, Phishing, Phone Phreaking, Programming Language/Protocol (specify), Repair, Robotics, Social Networking, Speed Reader, Stealth, Surveillance, Trolling, Video Editing, Video Games
WWPHITM? Amy Acker, Dan Ackroyd, Casey Affleck, Anthony Anderson, Jack Black, Tom Braidwood, Jeff Bridges, Matthew Broderick, Michael Cera, John Cho, David Cross, Johnny Depp, Zooey Deschanel, Janeane Garofalo, Jeff Goldblum, Seth Green, Dean Haglund, Anthony Hale, Tony Michael Hall, Alyson Hannigan, Bruce Harwood, Howard Hesseman, John Hodgman, Phillip Seymour Hoffman, Hugh Jackman, Val Kilmer, Fran Kranz, Justin Long, Allison Mack, John Oliver, Timothy Olyphant, Harold Ramis, Robert Redford, Christian Slater, Kevin Smith, Brent Spiner, Ethan Suplee, Rachael Taylor, Naomi Watts, Rain Wilson
Tag Line: “Cyberspace. A consensual hallucination experienced daily by billions of legitimate operators, in every nation, by children being taught mathematical concepts… A graphic representation of data abstracted from banks of every computer in the human system. Unthinkable complexity. Lines of light ranged in the nonspace of the mind, clusters and constellations of data. Like city lights, receding…”—William Gibson, Neuromancer
Tools of the Trade: Most hackers are pretty useless without a computer. Fortunately, movies have long established that hackers can perform amazing feats regardless of whether they’re using a top-of-the line supercomputer or a Commodore 64. For more realistic games, the GM may assign modifiers based on the quality of equipment being used. Hackers in cyberpunk and other futuristic games may interact with the network through virtual reality interfaces by using peripherals or through direct interfaces to their brains. Most hackers have a keen interest in emerging technology and those who can afford it collect all sorts of high-tech electronic gizmos.
Where You’ll Find Him: In front of the computer. While some hackers (especially those with social engineering skills) have some skills that beneficial in the field, the hacker is most useful when he’s online. A common trope in fiction is to have the hacker communicate with the team via two-way radio while he monitors progress, looks up information, and takes control of networked devices from a reasonably secure location.
Social Circle: Most of the hacker’s contacts will be online friends. These will often be people who he has never met and who are known only by their screen name. Depending on the nature of his work, the hacker may also have contacts in the computer industry, government, or criminal subculture.
Sample Character
Barbara “Oracle” Gordon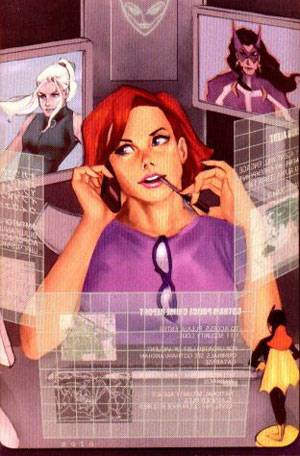
Body: 13
Brain: 16
Nerve: 15
Job: Super-Hero Support (16)
Gimmick: Despite the wheelchair, she’s still Batgirl (16)
Weakness: Quadriplegic (16)
Skills: Contacts +3; Library Science +2; Self-Defense +1
WWPHTIM? Emma Stone [Note: This is actually my choice for Batgirl. My first choice for Oracle-era Babs would be Uma Thurman, but I can’t in good conscience recommend her for any Bat-related role due to her awful performance in Batman & Robin.]
Dumb Fact: Has control over 12 technologically advanced satellites built by Lex Luthor.
Tag Line: “I’m Oracle. I know everybody.”
HP: 16
YY: 3
Inspirational Materials
Books & Comics
Batman titles (Oracle, Tim Drake, The Calculator)
Cyberpunk: Outlaws and Hackers on the Computer Frontier by Katie Hafner and John Markoff
The Hacker Files (Jack Marshall)
Neuromancer by William Gibson (Case)
Snow Crash by Neal Stephenson (Hiro Protagonist)
Games
Cyberpunk
GURPS Cyberpunk
GURPS Cyberworld
Shadowrun
Music
Cyberpunk, Billy Idol
People & Organizations
The 414s
Chaos Computer Club
Kevin Mitnick
The Warelords
TV & Movies
Buffy the Vampire Slayer (Oz, Willow Rosenberg)
Dark Angel (Logan “Eyes Only” Cale)
The Italian Job (Lyle a.k.a. “The Napster”)
Live Free or Die Hard (Matthew Farrell, Thomas Gabriel, Warlock)
The Lone Gunmen (All of them, especially Langly)
Smallville (Chloe Sullivan)
Sneakers (Martin Bishop)
Swordfish (Stanley Jobson)
WarGames